Web Application Firewall (WAF)

How do enterprises protect web applications from modern cyber threats
Web Application Firewall (WAF) safeguards web applications and APIs against common and advanced application-layer attacks. By inspecting HTTP and HTTPS traffic in real time, WAF helps enterprises defend against vulnerabilities, malicious bots, and unauthorized access ensuring secure and reliable digital experiences.
Why Web Application Firewall for enterprise applications

Protection Against OWASP Threats
Defends applications against SQL injection, cross-site scripting (XSS), command injection, and other OWASP Top 10 vulnerabilities.
Real-Time Traffic Inspection
Monitors and filters HTTP/HTTPS traffic to detect and block malicious requests before they reach applications.
Bot & Abuse Protection
Identifies and mitigates malicious bots, scraping attempts, and abnormal traffic behavior.
Policy-Based Security Controls
Apply customizable security rules tailored to application behavior and risk tolerance.
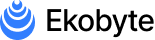
High Availability & Performance
Cloud-native architecture ensures protection without impacting application performance or availability.
Why Choose Indus Cloud for Web Application Firewall
Integrated Cloud Security Stack
Works seamlessly with Cloud Firewall, Load Balancer, ECS, and security services.
Enterprise-Level Threat Intelligence
Continuously updated rule sets to protect against emerging threats.
Scalable, Cloud-Native Protection
Designed to handle high-traffic enterprise applications without degradation.
Expert Security Support
Backed by experienced security professionals who manage and optimize protection.
What Web Application Firewall capabilities are available?

HTTP/HTTPS Protection
HTTP/HTTPS Protection
Managed Security Rules
Managed Security Rules

Custom Rule Configuration
Custom Rule Configuration

Attack Logging & Alerts
Attack Logging & Alerts
How We Deploy Web Application Firewall for You

1. Application & Threat Assessment
We review your web applications, traffic patterns, and exposure points to identify relevant security risks.
2. WAF Configuration & Policy Setup
WAF is configured with managed and custom rules aligned to your application requirements.
3. Traffic Validation & Tuning
Security policies are tested and fine-tuned to minimize false positives while maintaining strong protection.
4. Continuous Monitoring & Updates
Ongoing monitoring and rule updates ensure protection against evolving application threats.
Secure your web applications against modern threats
Protect applications, APIs, and digital platforms with enterprise-grade web security.